Welcome to our new webinar series!
We launched in collaboration with RegulX, a new series of webinars exploring how data-driven strategies and solutions can protect telecom operators and regulators against fraud and revenue loss.
In Episode 1: Simbox Fraud Unmasked: How Data Monitoring Can Stop Illegal Call Termination, we explored how Simbox fraud undermines both operators and regulators and how advanced analytics, machine learning, and policy reform can fight back.
We had excellent engagement during the session, and in this article, we provide a recap of the key questions asked by the participants and our experts responses
Key questions from the webinar and our responses
Q1: How does Simbox fraud affect telecom operators? Should operators block suspicious SIMs immediately or investigate first?
Simbox fraud significantly impacts telecom operators by diverting international incoming traffic through local SIM cards instead of legal interconnect routes. This bypasses termination fees and leads to:
Revenue loss: Operators and governments miss out on legitimate interconnect fees and taxes.
Network degradation: SIM boxes generate large volumes of short-duration calls that overload radio resources.
Regulatory risks: Undeclared revenues can lead to non-compliance with national regulations.
Customer experience issues: Poor call quality, unidentifiable caller IDs, and blocked international numbers can erode trust in the network.
As for whether to block the subscriber immediately or investigate further, the best practice is a risk-based approach:
Do not block immediately without confirmation.
Many fraud detection systems use machine learning or behavioral indicators (e.g., high number of short-duration calls, constant IMEI swapping, night-time activity), which can yield false positives—for instance, a call center or a user with high outbound call volume could be misidentified.
Recommended process:
- Flag the case in the fraud management system.
- Conduct investigation: Correlate IMSI, IMEI, Cell ID, call
- patterns, recharge behaviors, etc.
- If the evidence is strong and consistent with SIM box usage, apply graduated measures:
- First, disable outbound international calls or reduce QoS temporarily.
- Notify internal compliance or fraud teams.
- Block the SIM or IMEI only if the fraudulent behavior is confirmed.
This ensures fraud is stopped while avoiding negative impacts on innocent subscribers or legitimate businesses.
Second Approach: Progressive Service Degradation via IN or OCS
Instead of immediately blocking the SIM at the HLR or HSS or forcing an IMSI detach—which often alerts fraudsters and prompts them to rapidly replace the SIM—operators can opt for a more discreet and controlled method by altering the subscriber’s service profile in the Intelligent Network (IN) or Online Charging System (OCS).
By assigning the suspected SIM to a low-quality or restricted service class, the operator can degrade its performance (e.g., limit call duration, disable international access, reduce available credit or QoS) without completely cutting off service. This approach disrupts the effectiveness of the SIM Box while remaining under the radar, allowing further monitoring and investigation. If the suspicion is confirmed, the operator can then escalate to a full block or blacklist the subscriber and associated equipment.
This method provides a non-intrusive, reversible, and intelligence-driven alternative that helps balance fraud prevention with customer experience and investigative needs.
Q2: How does Simbox fraud impact telecom regulators?
SIM Box fraud weakens the regulator’s ability to collect revenue, enforce policy, ensure national security, and maintain a fair and transparent telecom market. Here are some major impacts of SIM Box Fraud on Regulators
Loss of Tax Revenue:
Regulators often impose levies on international call termination, such as:
- International Gateway License Fees
- Interconnect Taxes or Surtaxes
- Universal Service Fund contributions.
When SIM Box fraud diverts this traffic to local SIMs, these revenues go uncollected, resulting in significant fiscal losses for the state.
Distorted Traffic Statistics
Regulators rely on accurate traffic data to:
- Monitor national/international voice volumes
- Make policy and pricing decisions
- Assess operator compliance
SIM Box activity conceals the true volume of international incoming calls, misleading reports and degrading the quality of regulatory oversight.
Quality of Service (QoS) Complaints
Simbox grey routes often cause:
- Call setup failures
- One-way audio or poor voice quality
- Incorrect caller ID (due to CLI spoofing).
This leads to public dissatisfaction and blame on legitimate operators, even when they’re not at fault.
Undermining Legal and Security Frameworks
Simbox operations can:
- Bypass lawful interception, since traffic is masked as local
- Compromise national security, by making it harder to trace international callers
- Facilitate fraudulent or criminal communications under the radar
Market Disruption and Unfair Competition
Licensed operators pay regulatory fees, taxes, and invest in infrastructure. Simbox fraud allows illegal actors to:
- Compete unfairly by avoiding these costs
- Degrade market trust, especially in countries with heavy international call volumes
Q3: How much historical data is needed to apply ML/AI for SIM Box detection?
To effectively apply Machine Learning (ML) and AI to detect SIM Box fraud, the amount and type of historical data needed depends on the detection technique used, but here’s a clear guideline based on industry best practices:
Minimum Historical Data Requirements
Time Span
At least 30 to 90 days of call records is recommended to:
- Capture different usage patterns (e.g., weekends vs weekdays, holidays)
- Detect evolving fraud behavior and test longevity of SIMs
Some fraudsters rotate SIMs every 24–72 hours, so a longer history is key to identifying short-lived but repetitive usage patterns.
Volume of Records
Millions of CDRs (Call Detail Records) — ideally covering:
- All outgoing and incoming calls
- International traffic
- Cell IDs and location changes
- IMSI, IMEI, MSISDN relationships
The more events per SIM, the better the model’s confidence and precision.
To train ML models effectively, these data attributes are typically used:
- Subscriber Behavior Number of calls per day, unique numbers called, call durations, recharge patterns
- Device Behavior IMEI changes, device type, dual-SIM usage
- Location Behavior Number of unique Cell IDs visited, mobility patterns
- Call Routing Percentage of international-to-local calls, missing CLI, night-time calling patterns
- Network Events Failed calls, dropped calls, signaling anomalies
Model Types and Their Data Needs
- Supervised ML (e.g., Random Forest, XGBoost) Needs labeled dataset (fraud vs non-fraud SIMs), 30–90 days of labeled history is ideal
- Unsupervised ML (e.g., Clustering, Isolation Forest) Works with unlabeled data, but requires broader history (60+ days) to learn normal vs abnormal patterns
- Semi-Supervised or Hybrid AI Can combine expert rules with limited labeled data, efficient in telecom scenarios
Q4: Do you use supervised ML? Can Test Call Generation (TCG) results be used?
Yes, supervised ML methods are a core part of modern Simbox detection frameworks.
We often use supervised learning techniques when we have access to labeled data, particularly from:
Test Call Generation (TCG) Results
These are “ground truth” indicators of Simbox activity.
When a test call is terminated via a local SIM instead of the international gateway, it’s a confirmed bypass. These confirmed fraud events are labeled and used to train classification models.
Feedback Loop from Investigations
When fraud analysts confirm a SIM is fraudulent (even without TCG), this label is fed back into the ML pipeline to improve the model. This allows the system to learn and adapt over time to new tactics used by fraudsters.
Input Features (from CDRs, signaling, usage patterns):
- Number of calls per SIM
- Call duration statistics
- Ratio of unique B numbers
- Recharge patterns
- Cell ID changes
- IMEI–IMSI correlation
- Time-of-day usage patterns
Model Types Used:
- Random Forest
- XGBoost
- Logistic Regression
- Neural Networks (for large datasets)
In practice, we use a hybrid approach:
- Supervised ML: trained on confirmed cases (e.g., TCG, Human in the loop, blacklisted SIMs)
- Unsupervised ML: used to flag unknown patterns or zero-day frauds
- Rule-based detection: for instant blocking of obvious, high-risk behavior
Q5: What are the different types of SIM Box fraud setups?
Basic / Standalone SIM Box

A small physical device with slots for a limited number of SIM cards (typically 4–32). Often sold online as “VoIP gateways” or “GSM gateways.”
Key Features:
- Usually installed in homes, small offices, or hidden locations
- Uses local mobile SIM cards to terminate international calls
- Controlled remotely via a basic web interface or mobile signal
Fraud Risk:
Low to medium. Easier to detect due to static behavior, lack of sophisticated anti-detection features, and limited mobility.
Enterprise / High-Capacity SIM Box
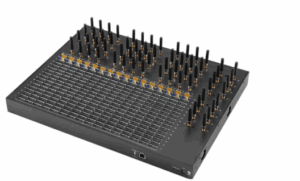
A larger, more professional-grade system with hundreds to thousands of SIM slots, built for industrial-scale bypass operations.
Key Features:
- Rack-mounted hardware in data centers or disguised installations
- Advanced SIM rotation, IMEI spoofing, and call traffic balancing
- Centralized control panel with fraud evasion tactics
Fraud Risk:
High. These systems can simulate human behavior, change IMEI per call, and spread SIM usage across multiple cells, making detection more difficult.
A telco or service provider may offer an Enterprise GSM Gateway (which resembles a high-capacity SIM Box) to business clients like:
- Call centers
- Bulk SMS providers
- Corporate customers
Legal use cases require:
- Authorization from the telecom regulator
- SIMs that are properly registered and assigned for business use
- Traffic declared and billed at correct interconnect rates
- Gateway registered as part of the telco’s licensed infrastructure
- No bypass of international interconnect or regulatory fees
In such cases, the device is marketed as a GSM Gateway, Fixed Cellular Terminal (FCT), or Corporate SIM Gateway, and the operator is responsible for ensuring compliance.
Software-Based SIM Box (Virtual SIM Box)
A purely virtual or cloud-hosted system that emulates SIM cards and GSM modems via APIs or remote SIM provisioning (via eSIM or OTA platforms).
Key Features:
- No physical SIMs—uses soft SIMs or remote SIM provisioning
- Often integrated with OTT apps, SIP gateways, or cloud PBX
- Highly stealthy; difficult to locate physically
Fraud Risk:
Very high. Hard to detect using traditional RF techniques or drive tests. Requires core network-level analytics and signaling layer monitoring to uncover.
Hybrid SIM Box
A combination of hardware and software systems designed to balance capacity, stealth, and flexibility. It may use physical SIMs but be controlled via cloud-based systems with advanced fraud evasion features.
Key Features:
- Can switch between physical and virtual SIM modes
- Remote SIM provisioning, SIM bank integration, and IMEI cycling
- Deployed in multiple countries to evade geolocation-based detection
Fraud Risk:
Very high. These systems blend techniques and may use IP tunneling, VPNs, and multi-country routing, making them resilient to localized countermeasures.
Q6: Besides call volume, what indicators reveal Simbox fraud
While high call volumes are a common red flag, modern Simbox detection relies on multi-dimensional behavioral and technical indicators, including:
Call Behavior Patterns
- High ratio of unique called numbers per SIM
- Predominantly short-duration calls (e.g., <10 seconds)
- Repetitive use of same B numbers across multiple SIMs
- No or low inbound activity (SIMs mostly send calls but never receive)
Device Usage Patterns
- Same IMEI used by multiple IMSIs (IMEI spoofing or fixed device)
- Frequent IMEI changes per SIM (anti-detection evasion)
- Static location despite long active periods (suggesting Simbox rig)
Mobility & Cell Site Analysis
- SIM remains in 1–2 cell towers for long periods (lack of human mobility)
- No handovers or mobility events typical of human usage
- Many SIMs operating from same cell at the same time, showing “cell crowding”
Temporal Patterns
- Calls made in unnatural hours (e.g., consistently between 2AM–6AM)
- Regular intervals between calls, suggesting automation
- Rapid call setup and teardown with minimal gaps
Recharge and Usage Behavior
- Use of low-value recharges in bulk (e.g., multiple $1 top-ups)
- No use of data or SMS — only voice
- Short SIM lifecycle (used for 1–3 days and discarded)
Q7:What if the Simbox fraud is in a country that you have very little traffic from ? or the traffic spread out evenly ?
Simbox fraud can still be detected with low traffic volumes if you focus on per-SIM behavioral anomalies rather than just volume.
Profile each SIM independently
- Does the usage resemble a human or a machine?
- Is the calling pattern consistent with normal customer behavior?
- Even 10–15 calls per day can be suspicious if they all follow a robotic pattern.
Use clustering or anomaly detection models
- Unsupervised models (e.g., DBSCAN, Isolation Forest) don’t need labels or heavy history
- They identify outliers based on peer behavior even in small datasets
Leverage cross-operator and regional patterns
- A single operator may have low traffic from a fraud source, but regional aggregation (via regulator monitoring) reveals the fraud more clearly
- Fraud networks often use multiple operators in parallel, which makes cross-operator correlation critical
Q8: What if no traditional SIMs are used?
As Simbox fraud has evolved, fraudsters have moved beyond traditional SIM cards, using techniques like eSIMs, remote SIM provisioning, rogue MVNO access, or even OTT-to-GSM bridges to bypass traditional detection methods. Here are some tools and techniques to detect modern Simbox Fraud (Without Traditional SIMs):
Signaling Analytics (SS7 / Diameter / SIP Monitoring)
Especially useful when SIMs are remote, virtual, or controlled via cloud infrastructure.
Detects anomalies in call setup signaling (e.g., MAP, ISUP, SIP)
Flags patterns like:
- Mismatched IMSI–IMEI pairs
- Static IMEI usage across dynamic locations
- Irregular location updates (LUs) or missing VLR updates
Tools: Signaling probe / Wireshark
CDR-Based Machine Learning and Behavioral Profiling
Even if physical SIMs aren’t present, call behavior still leaves a trace.
Track:
- High volume of short-duration calls (1–10 sec)
- High ratio of unique called numbers
- Frequent calls during night hours
- Inbound international call mapped to local number via “clean path”
Tools:
- Custom Spark/Big Data pipelines
- ML models (Isolation Forest, Clustering, Random Forest)
Core Network Data Correlation
Detect soft SIM activity or remote SIM hosting by analyzing inconsistencies in:
- IMSI–IMEI–CellID correlation
- Geolocation patterns: same IMSI appears in multiple cities in minutes (impossible travel)
- SIM presence without expected radio signaling events (e.g., no RRC or attach procedures)
If the subscriber is active in the core, but there’s no corresponding radio trace in the RAN, it’s likely using a remote or virtual SIM.
IMEI / TAC Validation
Many soft SIMs and OTT apps:
- Spoof or reuse fixed IMEIs
- Use non-GSMA-issued TACs (Type Allocation Codes)
Use IMEI validation tools or GSMA TAC databases to:
- Flag virtual devices
- Identify fixed IMEI patterns reused across many accounts
Deep Packet Inspection (DPI) and IP Analysis
To detect VoIP-to-GSM fraud, DPI can:
- Identify encrypted SIP tunnels, VPNs, or traffic to/from OTT apps
- Locate high-throughput SIP or RTP streams that don’t match user behavior
Especially useful at the operator or international gateway level.
Q9: Beyond arrests, what can regulators do?
Regulators play a critical strategic role in combating Simbox fraud beyond just arresting offenders. While enforcement is important, long-term success requires systemic actions, policy reforms, and technical oversight. Here’s a breakdown of what regulators can and should do:
Strengthen Regulatory Frameworks
Enforce strict SIM registration (KYC) rules
- Require biometric verification or national ID linkage
- Monitor and audit SIM issuance by operators and resellers
- Penalize operators who allow bulk SIM sales without compliance
Define clear policies on GSM gateways and VoIP termination
- Mandate licenses for legal use of GSM gateways (e.g., in call centers)
- Prohibit use of unregistered devices for call termination
- Publish a whitelist of legal devices and service providers
Implement Centralized Monitoring Systems
- Deploy national traffic monitoring platforms
- Collect CDRs, signaling, and financial data in near-real-time
- Detect anomalies such as:
- High volumes of short-duration calls
- Mismatched call routing paths (international > local)
- CLI spoofing
Use AI and Big Data analytics
- Correlate data from multiple operators
- Track suspicious IMEI/IMSI behaviors
- Monitor for “impossible travel” or repeated fraud patterns
Increase Inter-Agency Collaboration (Co Regulation)
Work with:
- Law enforcement (for raids and arrests)
- Customs (to stop illegal GSM gateway imports)
- Financial authorities (to monitor suspicious cash flow)
- Cybercrime units (to track virtual fraud networks)
Hold Operators Accountable
Require them to:
- Deploy fraud management systems (FMS)
- Report SIM Box detections and actions taken
- Implement anti-SIM rotation and IMEI filtering techniques
- Share real-time data feeds to the regulator
Audit their:
- SIM sales records
- Interconnect declarations
- Revenue from international traffic
Raise Public and Industry Awareness
- Run awareness campaigns for consumers about spoofed numbers and illegal termination
- Educate resellers and SMEs on what constitutes illegal VoIP/GSM gateway use
- Organize industry workshops to promote collaboration between MNOs and regulators
Control Device & Number Ecosystem
- Enforce IMEI registration and blacklisting of illegal devices
- Work with GSMA TAC database to validate devices in the network
- Impose CLI integrity requirements at the international gateway level
Cooperate Regionally and Internationally
Simbox fraud is often transnational:
- Share intelligence with regulators in other countries
- Create joint task forces or regional fraud detection hubs
- Collaborate on gateway-level CLI validation and traffic tracebacks
Regulators must evolve from being just enforcers to becoming data-driven oversight bodies. Arrests help in the short term, but lasting impact comes from policy enforcement, technical monitoring, inter-agency cooperation, and industry accountability.
Conclusion
Episode 1 of our webinar series, Simbox Fraud Unmasked, sparked an essential conversation around using data to combat illegal call termination. From understanding key data sources like IN, MSC, and probes to designing effective reconciliation models, it’s clear that revenue protection starts with visibility. Whether you’re a regulator, network operator, or analytics provider, actionable data is your strongest ally.
Missed the live session? Watch the replay
Coming Up Next: May 22 at 10:00 AM UTC+1
Webinar: CLI Spoofing Exposed: Protecting Call Identity and Revenue with Data-Powered Strategies
In Episode 2, we will explore the growing threat of Caller Line Identification (CLI) spoofing.
Learn how fraudsters manipulate CLI to bypass international tariffs and how real-time data monitoring and signaling integrity can stop them in their tracks. Register here to secure your spot